Recently, we shared a post about a network of domains used in a JavaScript credit card stealing malware campaign. These domains are all hosted on the same server with the IP 8.208.15.67.
In addition to the domains used by the skimmers, the server also had two sites whose domains were clearly created for phishing two Canadian banks:
rbcroyalbank[.]com.ng - Real address of the Royal Bank of Canada is rbcroyalbank.com
www1-bmo[.]com.co - Online banking for the Bank of Montreal is www1.bmo.com.
Given that the goal of malware on e-commerce sites and bank phishing is to obtain payment details and steal money, it’s quite natural to see the same bad actors participating in both types of attacks.
Moreover, as Group IB wrote in April about the previous wave of these JS skimmers, this campaign is known for using fake Magento login pages on domains mimicking the domain names of the online stores they tried to compromise. So phishing and credit card skimmers complement each other very well.
Unlike other domains, where registrant details were hidden by privacy protection services, the rbcroyalbank[.]com.ng domain had public WHOIS information.
Creation Date: 2019-06-10
...
Registrant ID: 1319589-NIRA
Registrant Name: Julio Jaime
Registrant Organization: Media Lend, LLC
Registrant Email: medialand.regru@gmail.com
Most likely, this information is [mostly] fake—but it was enough to find another batch of phishing domains.
Fake Data:
While the data says the address is in Indiana, the zip code and city provided are in New Jersey.
The email “medialand.regru@gmail.com” suggests a connection to a Russian domain name registrar reg.ru. Most likely, it’s a dedicated email address used specifically for registering new domain names.
We used DomainBigData to search if anything else was associated with that medialand.regru account and found a whole bunch of other [mostly] phishing domains registered in 2019.
Here are just some of them:
Facebook
facebook-bay[.]com 2019-03-29 reg.com
facebook-s3[.]com 2019-04-04 reg.com
facebook-s2[.]com 2019-04-04 reg.com
facebook-s1[.]com 2019-04-04 reg.com
facebook-listings[.]com 2019-03-30 reg.com
facebook-listing[.]com 2019-03-30 reg.com
facebook-itm[.]com 2019-03-30 reg.com
facebook-state[.]com 2019-03-29 reg.com
facebook-restore[.]com 2019-03-23 reg.com
restore-facebook[.]com 2019-03-23 reg.com
facebook-area[.]com 2019-03-17 reg.com
facebook-ss[.]com 2019-03-29 reg.com
recover-facebook[.]com 2019-03-23 reg.com
facebook-st[.]com 2019-03-29 reg.com
facebook-secure[.]com 2019-03-23 reg.com
static-facebook[.]com 2019-03-23 reg.com
facebook-us[.]com 2019-03-28 reg.com
facebook-s6[.]com 2019-04-20 reg.com
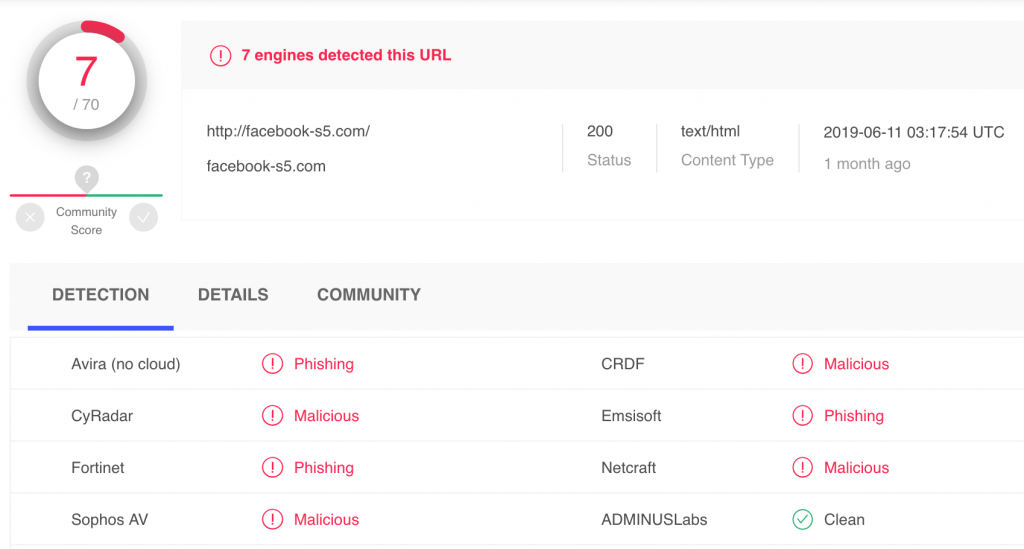
facebook-s5[.]com 2019-04-20 reg.com
facebook-s4[.]com 2019-04-20 reg.com
MyEtherWallet
myetherevvalliet[.]com 2019-07-21 reg.com
Bank phishing
carrefourbanque-compte[.]com 2019-06-18 reg.com
www-1royalbank[.]com 2019-05-29 reg.com
clickwebsite-rbc[.]com 2019-05-22 reg.com
tangerine-en[.]com 2019-05-07 reg.com
meine-db-account-i73983479[.]com 2019-04-08 reg.com
acc7201-statement-online[.]com 2019-04-01 reg.com
postecartaonline[.]com 2019-03-26 reg.com
client-sofinco[.]net 2019-03-01 reg.com
olb-secure[.]com 2019-02-20 reg.com
mabanquepro-bnpparibas[.]com 2019-03-17 reg.com
bmo-onlinebanking[.]com 2019-05-08 reg.com
secure-banking-updt[.]com 2019-02-22 reg.com
com-cgi-bin-3t5ufkygkl56-www-desjardins[.]com 2019-04-25 reg.com
PayPal
limited-services-paypal[.]com 2019-05-20 reg.com
restricted-users-paypai[.]com 2019-06-28 reg.com
Mobile carriers
my3-bill[.]com 2019-04-18 reg.com
three-mybilling[.]com 2019-03-28 reg.com
threebilling[.]com 2019-03-08 reg.com
myvodafone-billing[.]com 2019-03-12 reg.com
account-billing[.]com 2019-03-15 reg.com
Apple
apple-appield[.]com 2019-04-23 reg.com
apple-restore[.]com 2019-03-28 reg.com
Many of these domains have already been detected as phishing by various security companies:
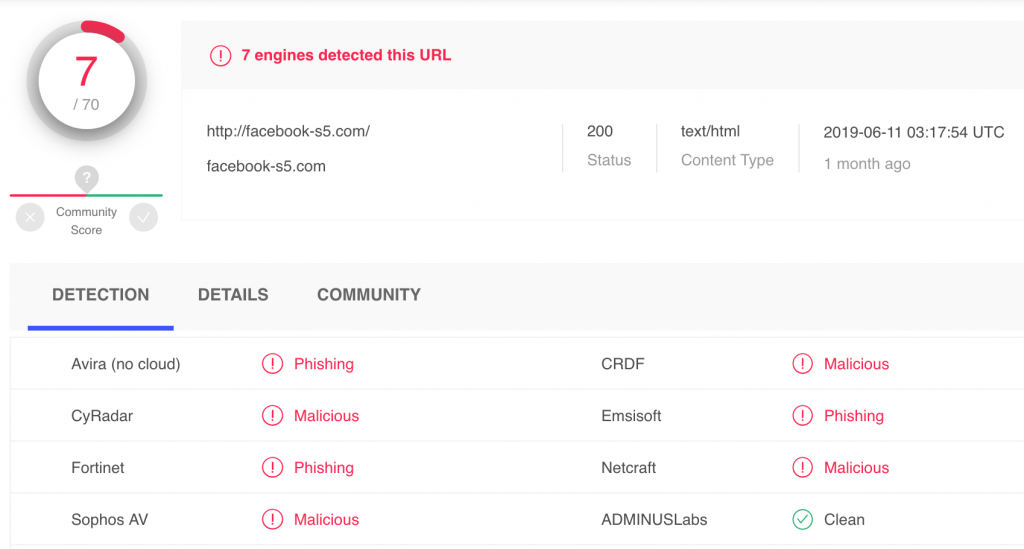
https://www.virustotal.com/gui/url/fb934dd5d574344759251678dd3c3b183f83fbe1cfb652201b155ee5c69a5476/detection