This is a simple way to know when a vulnerability in Plesk (or any other software) is being exploited in the wild:
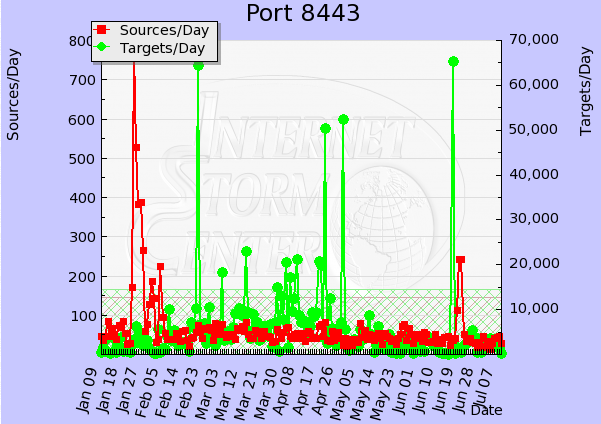
When the mass scans for it starts. The data is from ISC (isc.sans.org) and shows a massive increase in thenumber of queries for port 8443 (used by Plesk).