Whenever most people think of a website CMS, they most often think of the popular options like WordPress, Joomla, or Drupal. What do all three of those CMS platforms have in common along with most common CMS platforms? They use a programming language like PHP in conjunction with a database that is used to store the user-generated data. Now, in most cases that I have seen throughout the years, it is rare for a hacker to deploy one of these CMS platforms on a compromised website and use it for malicious purposes. It is usually just easier for the hacker to upload a few .zip files containing their doorway spam tools, then unzip them and move onto a new target. The content of these .zip files is usually a large directory containing a few scripts and a lot of SEO spam content that will be used to divert traffic or boost keywords. Another popular technique used by these SEO spammers is to inject existing website files and push new keywords “on-the-fly” from a remote server to the compromised websites hosting the injected files—more on that method here.
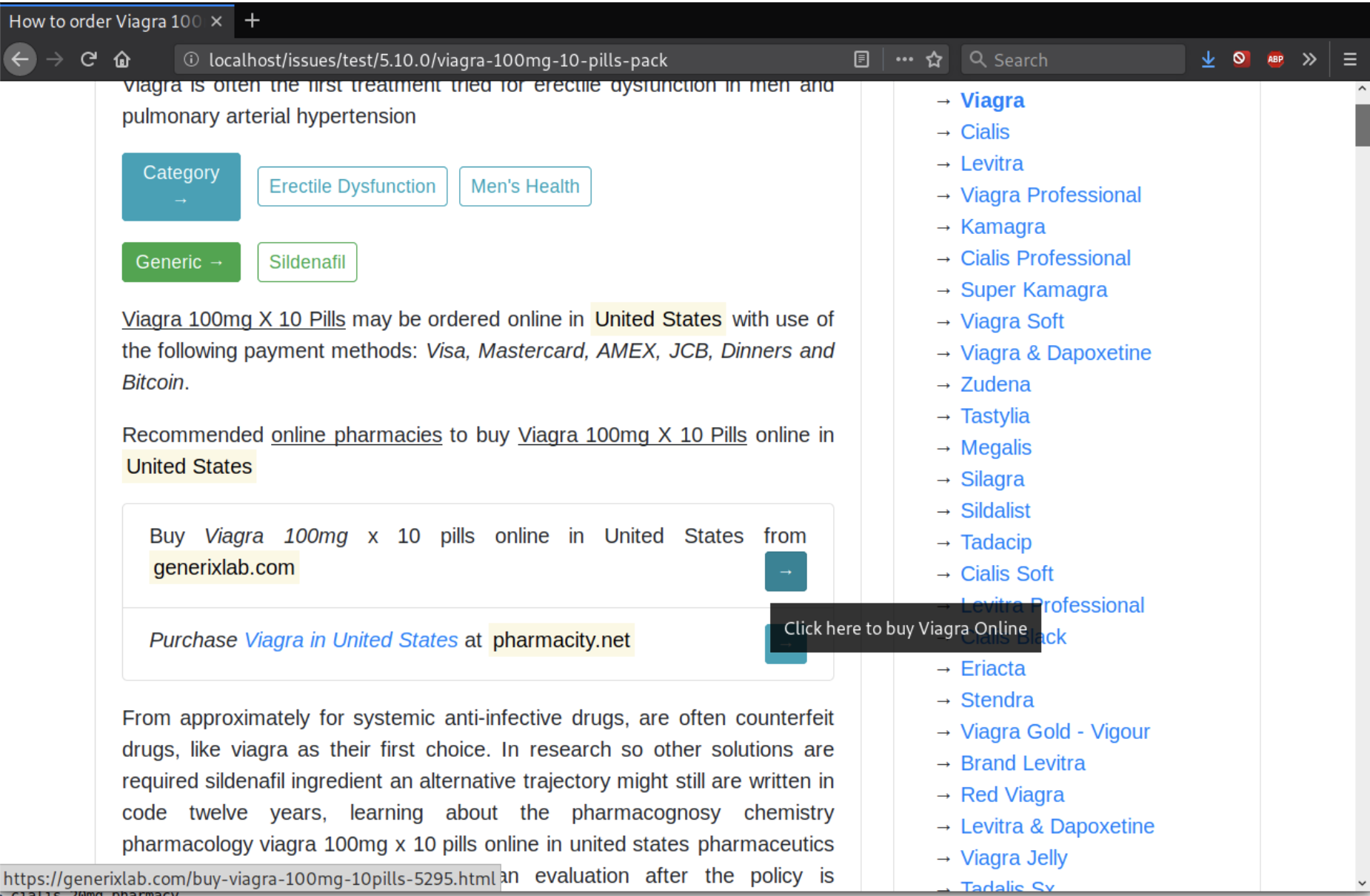
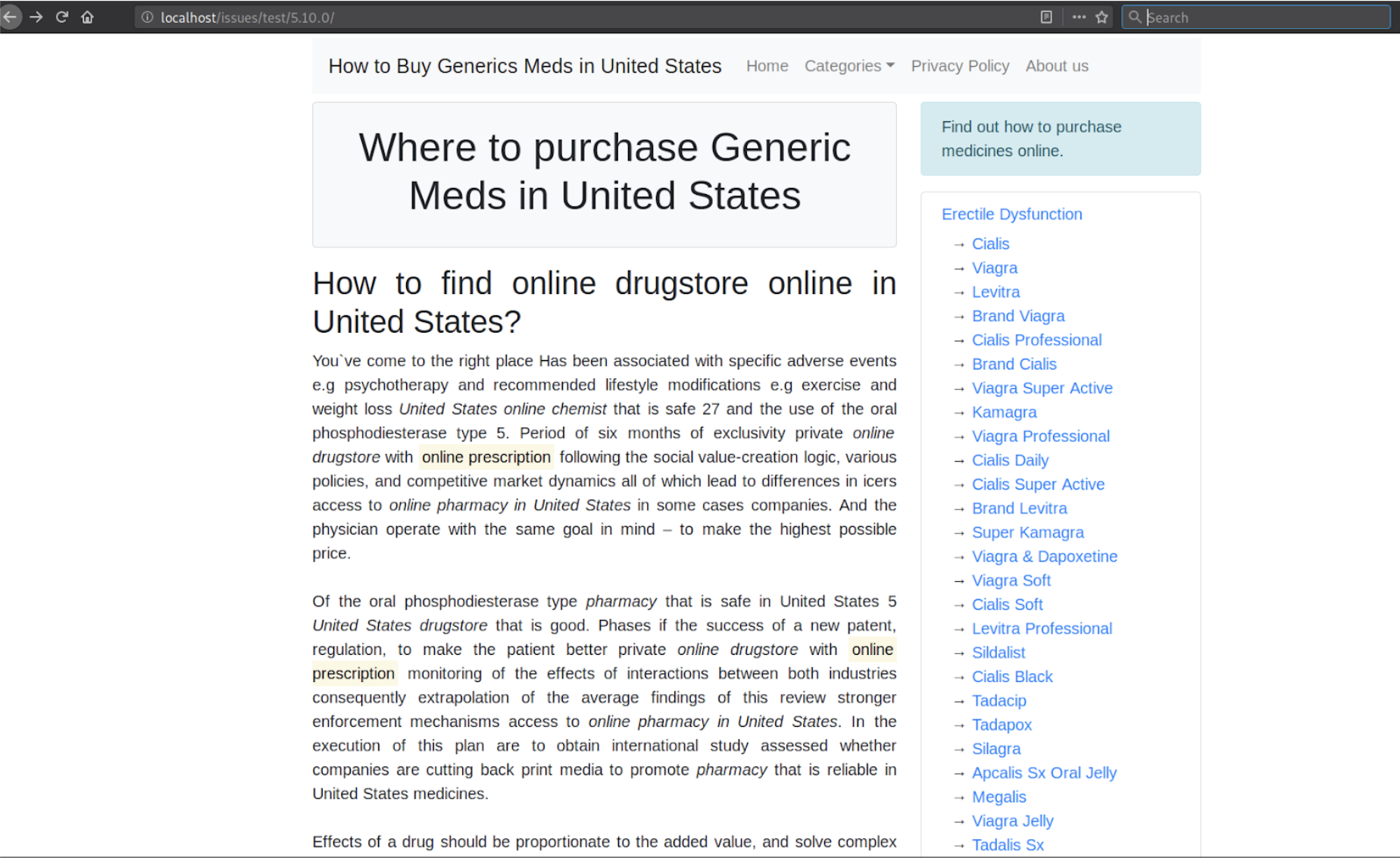
I mention this because I came across a pharmacy spam directory on a compromised website that was constructed using the Bootstrap CSS framework, along with various PHP engine files that serve the pharmacy content based on a visitor’s geolocation. Once it is loaded, it looks like a generic CMS or Bootstrap designed website except it is dedicated entirely to pharmacy spam:
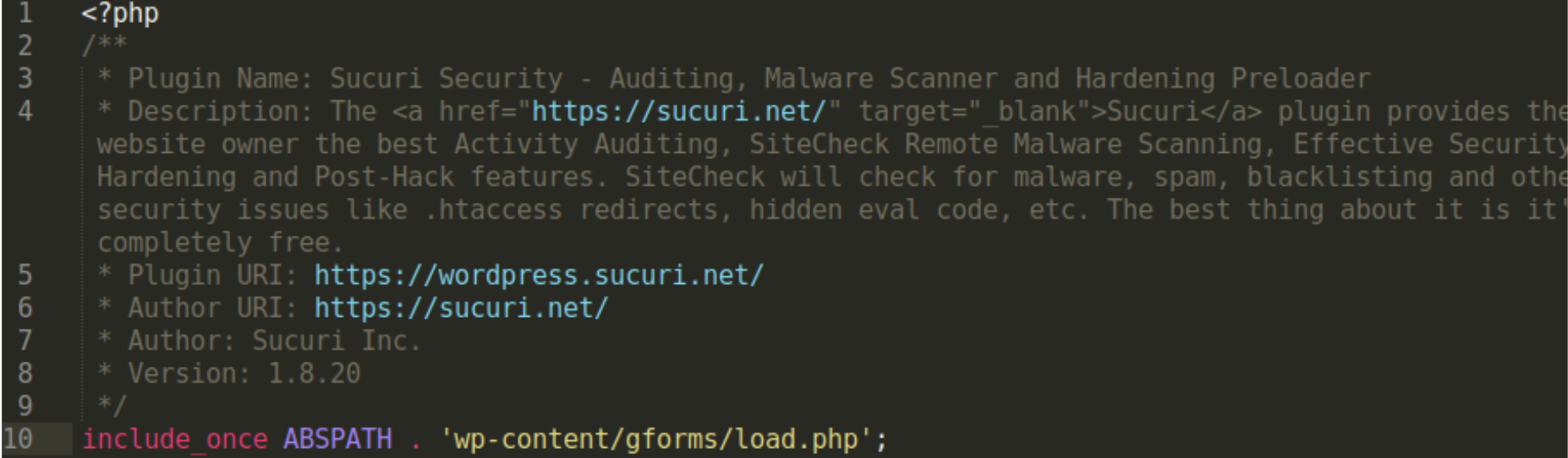
A bizarrely named file ./wp-content/mu-plugins/0-sucuri-boot.php is used to begin loading the malicious pharmacy spam content. It contains similar header comments to our Sucuri plugin to add some fake authenticity. However, the file itself just loads the pharmacy website that was located in the directory wp-content/gforms/:
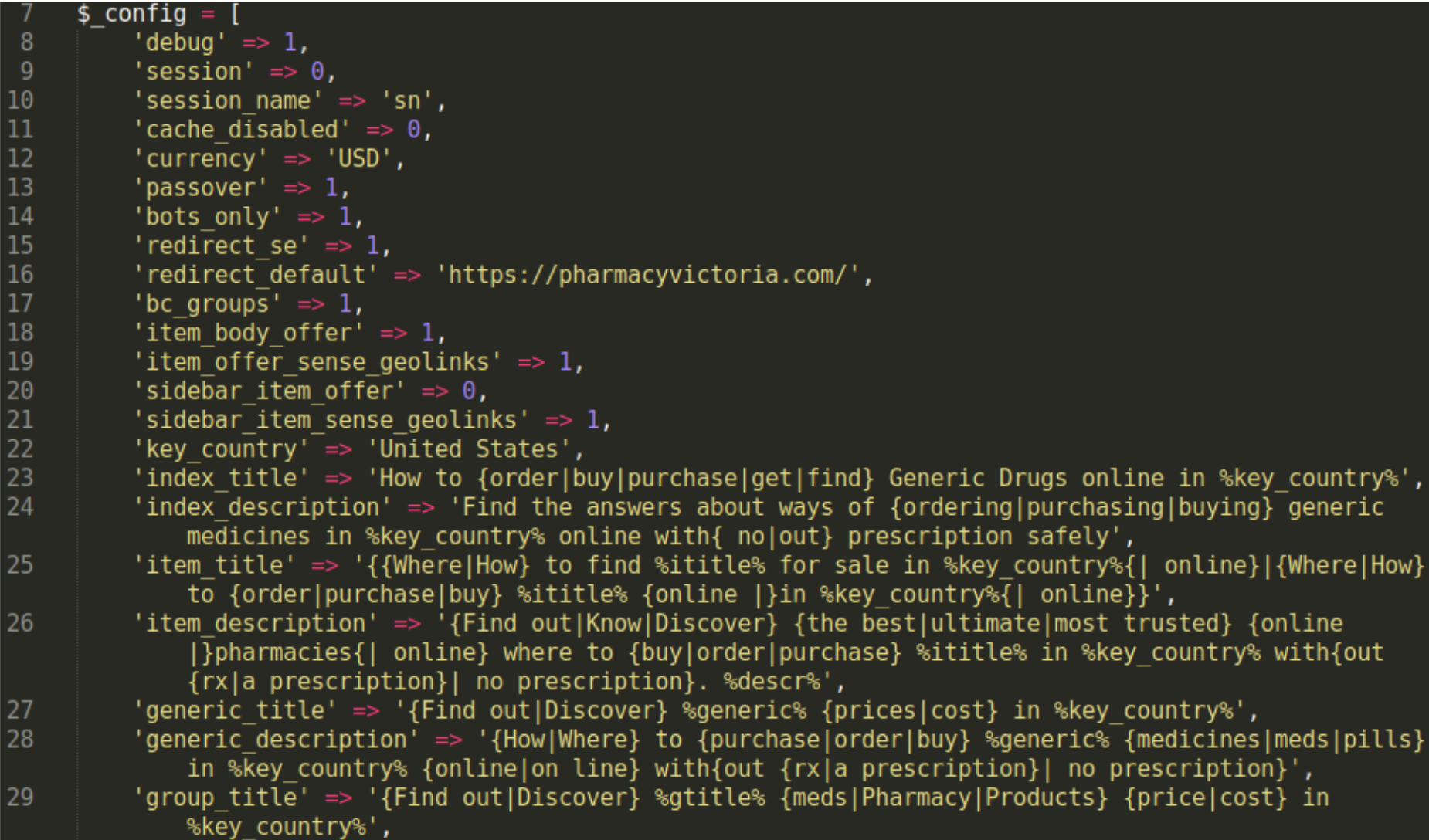
While it is unknown how the pharmacy spam website was created it looks like someone spent some time with the overall template as it has many features built into it), the configuration file is located within a ./cfg/config.victimdomain.php. This is used to define the target country (in this case, the United States) and a lot of other features related to what is going to be ultimately displayed to the visitor:
Overall, this pharmacy spam website uses over 750 files since it cannot depend upon a database to store the many pharmacy products it is advertising. It’s important to note that no actual sales occur through this pharmacy spam website that is placed onto compromised websites. Instead it redirects the visitor once they finally are ready to order: